You can configure an ASA to act as a DHCP server and assign dynamic IP addresses to requesting clients. The DHCP server can also generate dynamic DNS information, allowing DNS records to be updated dynamically as hosts require an IP address.
An ASA will return its own interface address for the client to use as the default gateway. The interface subnet mask is returned for the client to use as well. You can define and enable DHCP servers on more than one interface, if clients are located there.
Note that an ASA can only manage dynamic IP address assignments from its DHCP pool. Meaning, no reserved IP address for a specific client or network device (ip dhcp excluded-address in router IOS).
You can configure the DHCP server feature on the ASA via CLI using the following steps:
Step 1: Enable the DHCP server on an ASA interface that faces the clients:
ciscoasa(config)# dhcpd ?
configure mode commands/options:
address Configure the IP pool address range after this keyword
auto_config Enable auto configuration from client
dns Configure the IP addresses of the DNS servers after this
keyword
domain Configure DNS domain name after this keyword
enable Enable the DHCP server
lease Configure the DHCPD lease length after this keyword
option Configure options to pass to DHCP clients after this keyword
ping_timeout Configure ping timeout value after this keyword
update Configure dynamic updates
wins Configure the IP addresses of the NETBIOS servers after this
keyword
ciscoasa(config)# dhcpd enable ?
configure mode commands/options:
Available interfaces on which to enable the DHCP server:
inside Name of interface Vlan1
outside Name of interface Vlan2
Step 2: Create an address pool for clients on an interface:
ciscoasa(config)# dhcpd address ?
configure mode commands/options:
WORD IP address[es], <ip1>[-<ip2>]
Step 3: Configure DHCP options for clients.
You can use the dhcp option command to define any specific DHCP options that clients need to receive.
ciscoasa(config)# dhcpd option ?
configure mode commands/options:
<0-255> DHCP option code
ciscoasa(config)# dhcpd option 150 ?
configure mode commands/options:
ascii Configure the option information in ascii after this keyword
hex Configure the option information as a hexidecimal value after this
keyword
ip Configure the option information as IP address(es) after this keyword
<cr>
Step 4: Configure any global DHCP parameters.
ciscoasa(config)# dhcpd dns <dns1> <dns2>
ciscoasa(config)# dhcpd wins <wins1> <wins>
ciscoasa(config)# dhcpd domain <domain-name>
By default, each DHCP lease is sent with a lease time of 3600 seconds, or 1 hour. You can override that value globally with the following command:
ciscoasa(config)# dhcpd lease ?
configure mode commands/options:
<300-1048575> The length of lease, in seconds, granted to DHCP client from
the DHCP server, default is 3600
<cr>
Finally, when an ASA receives a DHCP request from a potential client, it looks up the next available IP address in the pool. Before a DHCP reply is returned, the ASA sends an ICMP echo (ping) as a test to make sure that the IP address is not already in use by some other host. By default, the ASA waits 50 ms for an ICMP reply; if no reply is received, it assumes that the IP address is indeed available and assigns it to the client. If an ICMP reply is received from that address, it knows that the address is already taken, so the next address from the pool is tried.
You can override the ping test timer by issuing the following command with a timeout (100 to 10,000) in milliseconds:
ciscoasa(config)# dhcpd ping_timeout ?
configure mode commands/options:
<10-10000> Ping timeout value in milli seconds, default is 50
<cr>
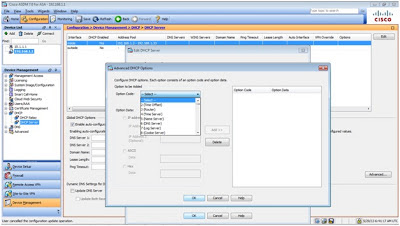
Here's what it looks like to configure a DHCP server using ASDM.
For this scenario, we configured the ASA to act as the DHCP server for the "inside" interface, run some debug and show commands for verification.
ciscoasa(config)# dhcpd ?
configure mode commands/options:
address Configure the IP pool address range after this keyword
auto_config Enable auto configuration from client
dns Configure the IP addresses of the DNS servers after this
keyword
domain Configure DNS domain name after this keyword
enable Enable the DHCP server
lease Configure the DHCPD lease length after this keyword
option Configure options to pass to DHCP clients after this keyword
ping_timeout Configure ping timeout value after this keyword
update Configure dynamic updates
wins Configure the IP addresses of the NETBIOS servers after this
keyword
ciscoasa(config)# dhcpd enable ?
configure mode commands/options:
Available interfaces on which to enable the DHCP server:
inside Name of interface Vlan1
outside Name of interface Vlan2
ciscoasa(config)# dhcpd enable inside
need to define address pool range first
dhcpd enable command failed
ciscoasa(config)# dhcpd address ?
configure mode commands/options:
WORD IP address[es], <ip1>[-<ip2>]
ciscoasa(config)# dhcpd address 192.168.10.10-192.168.10.254 ?
configure mode commands/options:
Available interfaces on which to enable the DHCP server:
inside Name of interface Vlan1
outside Name of interface Vlan2
ciscoasa(config)# dhcpd address 192.168.10.10-192.168.10.254 inside
Warning, DHCP pool range is limited to 32 addresses, set address range as: 192.168.10.10-192.168.10.41
ciscoasa(config)# dhcpd address 192.168.10.10-192.168.10.41 inside
ciscoasa(config)# dhcpd enable inside
ciscoasa(config)# dhcpd dns ?
configure mode commands/options:
Hostname or A.B.C.D IP address of server 1
ciscoasa(config)# dhcpd dns 192.168.10.20 ?
configure mode commands/options:
Hostname or A.B.C.D IP address of server 2
interface Specify interface to which action will apply to
<cr>
ciscoasa(config)# dhcpd dns 192.168.10.20 192.168.10.21
address overlap with dhcp pool ip addresses
Usage: dhcpd address <ip1>[-<ip2>] <srv_ifc_name>
dhcpd dns <dnsip1> [<dnsip2>] [interface <srv_ifc_name>]
dhcpd wins <winsip1> [<winsip2>] [interface <srv_ifc_name>]
dhcpd lease <lease_length> [interface <srv_ifc_name>]
dhcpd ping_timeout <timeout> [interface <srv_ifc_name>]
dhcpd domain <domain_name> [interface <srv_ifc_name>]
dhcpd option <code> {ascii <string> | hex <hex_string> |
ip <address_1> [<address_2>]} [interface <srv_ifc_name>]
dhcpd enable <srv_ifc_name>
dhcpd auto_config <clnt_if_name> [interface <srv_ifc_name>
dhcpd update dns [both] [override] [interface <srv_ifc_name>]
show dhcpd [binding|statistics]
clear dhcpd
clear dhcpd [binding|statistics]
ciscoasa(config)# dhcpd dns 192.168.1.20 192.168.1.21
ciscoasa(config)# dhcpd wins ?
configure mode commands/options:
Hostname or A.B.C.D IP address of server 1
ciscoasa(config)# dhcpd wins 192.168.1.22 192.168.1.23
ciscoasa(config)# dhcpd domain ?
configure mode commands/options:
WORD DNS domain name
<cr>
ciscoasa(config)# dhcpd domain lagura.com
ciscoasa(config)# dhcpd lease ?
configure mode commands/options:
<300-1048575> The length of lease, in seconds, granted to DHCP client from
the DHCP server, default is 3600
<cr>
ciscoasa(config)# dhcpd lease 86400
ciscoasa(config)# debug dhcpd event ?
<1-255> Specify an optional debug level (default is 1)
<cr>
ciscoasa(config)# debug dhcpd event
debug dhcpd event enabled at level 1
ciscoasa(config)# DHCPD: checking for expired leases.
DHCPD: checking for expired leases.
ciscoasa(config)# dhcpd_create_automatic_binding() adding NP rule for client 192.168.10.10
DHCPD: assigned IP address 192.168.10.10 to client 0178.2bcb.d4a0.85.
ciscoasa(config)# no debug dhcpd event
debug dhcpd event disabled.
ciscoasa(config)# ping 192.168.10.10
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.10.10, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 1/2/10 ms
ciscoasa(config)# show dhcpd ?
exec mode commands/options:
binding Show dhcp bindings
state Show dhcpd state
statistics Show dhcpd statistics
ciscoasa(config)# show dhcpd state
Context Configured as DHCP Server
Interface inside, Configured for DHCP SERVER
Interface outside, Configured for DHCP CLIENT
ciscoasa(config)# show dhcpd binding ?
exec mode commands/options:
all Show all dhcpd bindings
ciscoasa(config)# show dhcpd binding all
IP address Client Identifier Lease expiration Type
192.168.10.10 0178.2bcb.d4a0.85 86240 seconds Automatic
ciscoasa(config)# show dhcpd statistics
DHCP UDP Unreachable Errors: 0
DHCP Other UDP Errors: 0
Address pools 1
Automatic bindings 1
Expired bindings 0
Malformed messages 0
Message Received
BOOTREQUEST 0
DHCPDISCOVER 1
DHCPREQUEST 1
DHCPDECLINE 0
DHCPRELEASE 0
DHCPINFORM 1
Message Sent
BOOTREPLY 0
DHCPOFFER 1
DHCPACK 2
DHCPNAK 0
----
Ethernet adapter Local Area Connection:
Connection-specific DNS Suffix . : lagura.com
Description . . . . . . . . . . . : Realtek PCIe GBE Family Controller
Physical Address. . . . . . . . . : 78-2B-CB-D4-A0-85
DHCP Enabled. . . . . . . . . . . : Yes
Autoconfiguration Enabled . . . . : Yes
Link-local IPv6 Address . . . . . : fe80::4562:9b92:c15f:91ff%10(Preferred)
IPv4 Address. . . . . . . . . . . : 192.168.10.10(Preferred)
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Lease Obtained. . . . . . . . . . : Thursday, May 30, 2013 12:39:59 AM
Lease Expires . . . . . . . . . . : Friday, May 31, 2013 12:39:59 AM
Default Gateway . . . . . . . . . : 192.168.10.1
DHCP Server . . . . . . . . . . . : 192.168.10.1
DHCPv6 IAID . . . . . . . . . . . : 242756555
DHCPv6 Client DUID. . . . . . . . : 00-01-00-01-16-FF-27-59-78-2B-CB-D4-A0-85
DNS Servers . . . . . . . . . . . : 192.168.1.20
192.168.1.21
Primary WINS Server . . . . . . . : 192.168.1.22
Secondary WINS Server . . . . . . : 192.168.1.23
NetBIOS over Tcpip. . . . . . . . : Enabled
Using Wireshark to capture packets, we're able to observe the DHCP "DORA" process (Discover, Offer, Request, Ack).
Friday, June 21, 2013
Sunday, June 9, 2013
Configuring EtherChannel on an ASA
An EtherChannel (starting release 8.4), allows two or up to eight active physical interfaces to be bundled together and form a single logical port-channel interface. Each interface must be of the same type, speed, and duplex mode before an EtherChannel can be built.
To build an EtherChannel, the ASA and a switch must both agree to do so. The table below summarizes the EtherChannel negotiation methods and its characteristics.
EtherChannel Negotiation Methods
Negotiation Mode Negotiation Packets Sent? Characteristics
On No All ports channeling all the time
Passive Yes Waits to channel until asked
Active Yes Actively asks to form a channel
For this scenario, we built an EtherChannel between the ASA and a switch using the CLI:
ciscoasa(config)# interface gigabitethernet1
ciscoasa(config-if)# no shutdown
ciscoasa(config-if)# channel-group ?
interface mode commands/options:
<1-48> Channel group number
ciscoasa(config-if)# channel-group 1 ?
interface mode commands/options:
mode Etherchannel Mode of the interface
ciscoasa(config-if)# channel-group 1 mode ?
interface mode commands/options:
active Enable LACP unconditionally
on Enable static port-channel
passive Enable LACP only if a LACP device is detected
ciscoasa(config-if)# channel-group 1 mode on
INFO: security-level and IP address are cleared on GigabitEthernet1.
ciscoasa(config-if)# interface gigabitethernet2
ciscoasa(config-if)# no shutdown
ciscoasa(config-if)# channel-group 1 mode on
INFO: security-level and IP address are cleared on GigabitEthernet2.
ciscoasa(config-if)# show port-channel summary
Flags: D - down P - bundled in port-channel
I - stand-alone s - suspended
H - Hot-standby (LACP only)
U - in use N - not in use, no aggregation/nameif
M - not in use, no aggregation due to minimum links not met
w - waiting to be aggregated
Number of channel-groups in use: 1
Group Port-channel Protocol Ports
------+-------------+-----------+-----------------------------------------------
1 Po1(N) - Gi1(P) Gi2(P)
ciscoasa(config-if)# interface ?
configure mode commands/options:
GigabitEthernet GigabitEthernet IEEE 802.3z
Port-channel Ethernet Channel of interfaces
Redundant Redundant Interface
<cr>
ciscoasa(config-if)# interface port-channel ?
configure mode commands/options:
<1-48> Port-channel interface number
ciscoasa(config-if)# interface port-channel 1
ciscoasa(config-if)# port-channel ?
interface mode commands/options:
load-balance Load Balancing method
min-bundle Configure minimum number of active links
ciscoasa(config-if)# port-channel load-balance ?
interface mode commands/options:
dst-ip Dst IP Addr
dst-ip-port Dst IP Addr and TCP/UDP Port
dst-mac Dst Mac Addr
dst-port Dst TCP/UDP Port
src-dst-ip Src XOR Dst IP Addr
src-dst-ip-port Src XOR Dst IP Addr and TCP/UDP Port
src-dst-mac Src XOR Dst Mac Addr
src-dst-port Src XOR Dst TCP/UDP Port
src-ip Src IP Addr
src-ip-port Src IP Addr and TCP/UDP Port
src-mac Src Mac Addr
src-port Src TCP/UDP Port
vlan-dst-ip Vlan, Dst IP Addr
vlan-dst-ip-port Vlan, Dst IP Addr and TCP/UDP Port
vlan-only Vlan
vlan-src-dst-ip Vlan, Src XOR Dst IP Addr
vlan-src-dst-ip-port Vlan, Src XOR Dst IP Addr and TCP/UDP Port
vlan-src-ip Vlan, Src IP Addr
vlan-src-ip-port Vlan, Src IP Addr and TCP/UDP Port
ciscoasa(config-if)# port-channel load-balance src-dst-ip
ciscoasa(config-if)# port-channel min-bundle ?
interface mode commands/options:
<1-8> Number of minimum links
ciscoasa(config-if)# port-channel min-bundle 1
ciscoasa(config-if)# lacp ?
interface mode commands/options:
max-bundle Configure maximum number of active links
configure mode commands/options:
system-priority LACP priority for the system
ciscoasa(config-if)# lacp max-bundle ?
interface mode commands/options:
<1-8> Number of maximum links
ciscoasa(config-if)# lacp max-bundle 8
ciscoasa(config)# interface port-channel1
ciscoasa(config-if)# ip address 192.168.1.1 255.255.255.0
ciscoasa(config-if)# nameif inside
INFO: Security level for "inside" set to 100 by default.
ciscoasa(config-if)# show port-channel 1
Ports: 2 Maxports = 16
Port-channels: 1 Max Port-channels = 48
Protocol: ON
Minimum Links: 1
Load balance: src-dst-ip
ciscoasa(config-if)# show port-channel summary
Flags: D - down P - bundled in port-channel
I - stand-alone s - suspended
H - Hot-standby (LACP only)
U - in use N - not in use, no aggregation/nameif
M - not in use, no aggregation due to minimum links not met
w - waiting to be aggregated
Number of channel-groups in use: 1
Group Port-channel Protocol Ports
------+-------------+-----------+-----------------------------------------------
1 Po1(U) - Gi1(P) Gi2(P)
ciscoasa(config-if)# show port-channel detail
Channel-group listing:
-----------------------
Group: 1
----------
Ports: 2 Maxports = 16
Port-channels: 1 Max Port-channels = 48
Protocol: ON
Minimum Links: 1
Load balance: src-dst-ip
Ports in the group:
-------------------
Port: Gi1
------------
Port state = bndl
Channel group = 1 Mode = ON
Port-channel = Po1
Port: Gi2
------------
Port state = bndl
Channel group = 1 Mode = ON
Port-channel = Po1
ciscoasa(config-if)# ping 192.168.1.2
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.1.2, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 10/24/60 ms
----
SW1(config)#interface fastethernet1/1
SW1(config-if)#no shutdown
SW1(config-if)#channel-group ?
<1-6> Channel group number
SW1(config-if)#channel-group 1 ?
mode Etherchannel Mode of the interface
SW1(config-if)#channel-group 1 mode ?
on Enable Etherchannel only
SW1(config-if)#channel-group 1 mode on
Creating a port-channel interface Port-channel1
SW1(config-if)#
*Mar 1 00:01:19.231: %EC-5-BUNDLE: Interface Fa1/1 joined port-channel Po1
SW1(config-if)#
*Mar 1 00:01:22.111: %LINEPROTO-5-UPDOWN: Line protocol on Interface Port-channel1, changed state to up
SW1(config-if)#interface fastethernet1/2
SW1(config-if)#no shutdown
SW1(config-if)#channel-group 1 mode on
SW1(config-if)#
*Mar 1 00:01:35.187: %EC-5-BUNDLE: Interface Fa1/2 joined port-channel Po1
SW1(config-if)#do show etherchannel summary
Flags: D - down P - in port-channel
I - stand-alone s - suspended
R - Layer3 S - Layer2
U - in use
Group Port-channel Ports
-----+------------+-----------------------------------------------------------
1 Po1(SU) Fa1/1(P) Fa1/2(P)
SW1(config-if)#interface vlan1
SW1(config-if)#ip address 192.168.1.2 255.255.255.0
SW1(config-if)#do ping 192.168.1.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.1.1, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 4/22/56 ms
You can also configure an EtherChannel using the ASDM:
EtherChannel Negotiation Methods
Negotiation Mode Negotiation Packets Sent? Characteristics
On No All ports channeling all the time
Passive Yes Waits to channel until asked
Active Yes Actively asks to form a channel
For this scenario, we built an EtherChannel between the ASA and a switch using the CLI:
ciscoasa(config)# interface gigabitethernet1
ciscoasa(config-if)# no shutdown
ciscoasa(config-if)# channel-group ?
interface mode commands/options:
<1-48> Channel group number
ciscoasa(config-if)# channel-group 1 ?
interface mode commands/options:
mode Etherchannel Mode of the interface
ciscoasa(config-if)# channel-group 1 mode ?
interface mode commands/options:
active Enable LACP unconditionally
on Enable static port-channel
passive Enable LACP only if a LACP device is detected
ciscoasa(config-if)# channel-group 1 mode on
INFO: security-level and IP address are cleared on GigabitEthernet1.
ciscoasa(config-if)# interface gigabitethernet2
ciscoasa(config-if)# no shutdown
ciscoasa(config-if)# channel-group 1 mode on
INFO: security-level and IP address are cleared on GigabitEthernet2.
ciscoasa(config-if)# show port-channel summary
Flags: D - down P - bundled in port-channel
I - stand-alone s - suspended
H - Hot-standby (LACP only)
U - in use N - not in use, no aggregation/nameif
M - not in use, no aggregation due to minimum links not met
w - waiting to be aggregated
Number of channel-groups in use: 1
Group Port-channel Protocol Ports
------+-------------+-----------+-----------------------------------------------
1 Po1(N) - Gi1(P) Gi2(P)
ciscoasa(config-if)# interface ?
configure mode commands/options:
GigabitEthernet GigabitEthernet IEEE 802.3z
Port-channel Ethernet Channel of interfaces
Redundant Redundant Interface
<cr>
ciscoasa(config-if)# interface port-channel ?
configure mode commands/options:
<1-48> Port-channel interface number
ciscoasa(config-if)# interface port-channel 1
ciscoasa(config-if)# port-channel ?
interface mode commands/options:
load-balance Load Balancing method
min-bundle Configure minimum number of active links
ciscoasa(config-if)# port-channel load-balance ?
interface mode commands/options:
dst-ip Dst IP Addr
dst-ip-port Dst IP Addr and TCP/UDP Port
dst-mac Dst Mac Addr
dst-port Dst TCP/UDP Port
src-dst-ip Src XOR Dst IP Addr
src-dst-ip-port Src XOR Dst IP Addr and TCP/UDP Port
src-dst-mac Src XOR Dst Mac Addr
src-dst-port Src XOR Dst TCP/UDP Port
src-ip Src IP Addr
src-ip-port Src IP Addr and TCP/UDP Port
src-mac Src Mac Addr
src-port Src TCP/UDP Port
vlan-dst-ip Vlan, Dst IP Addr
vlan-dst-ip-port Vlan, Dst IP Addr and TCP/UDP Port
vlan-only Vlan
vlan-src-dst-ip Vlan, Src XOR Dst IP Addr
vlan-src-dst-ip-port Vlan, Src XOR Dst IP Addr and TCP/UDP Port
vlan-src-ip Vlan, Src IP Addr
vlan-src-ip-port Vlan, Src IP Addr and TCP/UDP Port
ciscoasa(config-if)# port-channel load-balance src-dst-ip
ciscoasa(config-if)# port-channel min-bundle ?
interface mode commands/options:
<1-8> Number of minimum links
ciscoasa(config-if)# port-channel min-bundle 1
ciscoasa(config-if)# lacp ?
interface mode commands/options:
max-bundle Configure maximum number of active links
configure mode commands/options:
system-priority LACP priority for the system
ciscoasa(config-if)# lacp max-bundle ?
interface mode commands/options:
<1-8> Number of maximum links
ciscoasa(config-if)# lacp max-bundle 8
ciscoasa(config)# interface port-channel1
ciscoasa(config-if)# ip address 192.168.1.1 255.255.255.0
ciscoasa(config-if)# nameif inside
INFO: Security level for "inside" set to 100 by default.
ciscoasa(config-if)# show port-channel 1
Ports: 2 Maxports = 16
Port-channels: 1 Max Port-channels = 48
Protocol: ON
Minimum Links: 1
Load balance: src-dst-ip
ciscoasa(config-if)# show port-channel summary
Flags: D - down P - bundled in port-channel
I - stand-alone s - suspended
H - Hot-standby (LACP only)
U - in use N - not in use, no aggregation/nameif
M - not in use, no aggregation due to minimum links not met
w - waiting to be aggregated
Number of channel-groups in use: 1
Group Port-channel Protocol Ports
------+-------------+-----------+-----------------------------------------------
1 Po1(U) - Gi1(P) Gi2(P)
ciscoasa(config-if)# show port-channel detail
Channel-group listing:
-----------------------
Group: 1
----------
Ports: 2 Maxports = 16
Port-channels: 1 Max Port-channels = 48
Protocol: ON
Minimum Links: 1
Load balance: src-dst-ip
Ports in the group:
-------------------
Port: Gi1
------------
Port state = bndl
Channel group = 1 Mode = ON
Port-channel = Po1
Port: Gi2
------------
Port state = bndl
Channel group = 1 Mode = ON
Port-channel = Po1
ciscoasa(config-if)# ping 192.168.1.2
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.1.2, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 10/24/60 ms
----
SW1(config)#interface fastethernet1/1
SW1(config-if)#no shutdown
SW1(config-if)#channel-group ?
<1-6> Channel group number
SW1(config-if)#channel-group 1 ?
mode Etherchannel Mode of the interface
SW1(config-if)#channel-group 1 mode ?
on Enable Etherchannel only
SW1(config-if)#channel-group 1 mode on
Creating a port-channel interface Port-channel1
SW1(config-if)#
*Mar 1 00:01:19.231: %EC-5-BUNDLE: Interface Fa1/1 joined port-channel Po1
SW1(config-if)#
*Mar 1 00:01:22.111: %LINEPROTO-5-UPDOWN: Line protocol on Interface Port-channel1, changed state to up
SW1(config-if)#interface fastethernet1/2
SW1(config-if)#no shutdown
SW1(config-if)#channel-group 1 mode on
SW1(config-if)#
*Mar 1 00:01:35.187: %EC-5-BUNDLE: Interface Fa1/2 joined port-channel Po1
SW1(config-if)#do show etherchannel summary
Flags: D - down P - in port-channel
I - stand-alone s - suspended
R - Layer3 S - Layer2
U - in use
Group Port-channel Ports
-----+------------+-----------------------------------------------------------
1 Po1(SU) Fa1/1(P) Fa1/2(P)
SW1(config-if)#interface vlan1
SW1(config-if)#ip address 192.168.1.2 255.255.255.0
SW1(config-if)#do ping 192.168.1.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.1.1, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 4/22/56 ms
You can also configure an EtherChannel using the ASDM:
Saturday, June 1, 2013
Manually Upgrading the ASA Software During a Reload
We usually go to ROMMON when performing a password recovery on the ASA or when its operating system is corrupted or accidentally deleted.
For this scenario, we'll be doing the latter and here are the steps for booting an ASA image file when in ROMMON mode:
Steps ROMMON Command
1. Interrupt the bootup sequence Press Esc or Break at the appropriate time
2. Identify an ASA interface where the rommon>interface <physical-name>
TFTP server is located.
3. Assign an IP address to the ASA interface. rommon>address <ip-address>
4. Assign a default gateway (optional) rommon>gateway <ip-address>
5. Identify the TFTP server address. rommon>server <ip-address>
6. Identify the image filename. rommon>file <filename>
7. Test connectivity to the TFTP server. rommon>ping <ip-address>
8. Issue the tftpdnld command rommon>tftpdnld
Evaluating BIOS Options ...
Launch BIOS Extension to setup ROMMON
Cisco Systems ROMMON Version (1.0(12)13) #0: Thu Aug 28 15:55:27 PDT 2008
Platform ASA5505
Use BREAK or ESC to interrupt boot.
Use SPACE to begin boot immediately.
Boot in 8 seconds // HIT ESC KEY
Boot interrupted.
Ethernet0/0 // CONNECTED TO FTP SERVER
MAC Address: c84c.7596.e7c6
Link is UP
Use ? for help.
rommon #0> ?
Variables: Use "sync" to store in NVRAM
ADDRESS= <addr> local IP address
CONFIG= <name> config file path/name
GATEWAY= <addr> gateway IP address
IMAGE= <name> image file path/name
LINKTIMEOUT= <num> Link UP timeout (seconds)
PKTTIMEOUT= <num> packet timeout (seconds)
PORT= <name> ethernet interface port
RETRY= <num> Packet Retry Count (Ping/TFTP)
SERVER= <addr> server IP address
VLAN= <num> enable/disable DOT1Q tagging on the selected port
Commands:
? valid command list
address <addr> local IP address
boot <args> boot an image, valid args are:
- "image file spec" and/or
- "cfg=<config file spec>"
clear clear interface statistics
confreg <value> set hex configuration register
dev display platform interface devices
erase <arg> erase storage media
file <name> application image file path/name
gateway <addr> gateway IP address
gdb <cmd> edit image gdb settings
help valid command list
history display command history
interface <name> ethernet interface port
no <feat> clear feature settings
ping <addr> send ICMP echo
reboot halt and reboot system
reload halt and reboot system
repeat <arg> repeat previous command, valid arguments:
- no arg: repeat last command
- number: index into command history table
- string: most recent 1st arg match in command history table
reset halt and reboot system
server <addr> server IP address
set display all variable settings
show <cmd> display cmd-specific information
sync save variable settings in NVRAM
tftpdnld TFTP download
timeout <num> packet timeout (seconds)
trace toggle packet tracing
unset <varname> unset a variable name
rommon #1> address 192.168.1.1
rommon #2> server 192.168.1.2
rommon #3> file asa901-k8.bin
rommon #4> ping 192.168.1.2
Sending 20, 100-byte ICMP Echoes to 192.168.1.2, timeout is 4 seconds:
?!!!!!!!!!!!!!!!!!!!
Success rate is 95 percent (19/20)
rommon #5> tftpdnld
ROMMON Variable Settings:
ADDRESS=192.168.1.1
SERVER=192.168.1.2
GATEWAY=0.0.0.0
PORT=Ethernet0/0
VLAN=untagged
IMAGE=asa901-k8.bin
CONFIG=
LINKTIMEOUT=20
PKTTIMEOUT=4
RETRY=20
tftp asa901-k8.bin@192.168.1.2
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
<output truncated>
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
Received 27260928 bytes
Launching TFTP Image...
Cisco Security Appliance admin loader (3.0) #0: Fri Oct 26 16:36:37 PDT 2012
Platform ASA5505
Loading...
IO memory blocks requested from bigphys 32bit: 9928
Àdosfsck 2.11, 12 Mar 2005, FAT32, LFN
Starting check/repair pass.
Starting verification pass.
/dev/hda1: 392 files, 26848/31033 clusters
dosfsck(/dev/hda1) returned 0
Processor memory 343932928, Reserved memory: 62914560
Total SSMs found: 0
Total NICs found: 10
88E6095 rev 2 Gigabit Ethernet @ index 09 MAC: 0000.0003.0002
88E6095 rev 2 Ethernet @ index 08 MAC: c84c.7596.e7c5
88E6095 rev 2 Ethernet @ index 07 MAC: c84c.7596.e7c4
88E6095 rev 2 Ethernet @ index 06 MAC: c84c.7596.e7c3
88E6095 rev 2 Ethernet @ index 05 MAC: c84c.7596.e7c2
88E6095 rev 2 Ethernet @ index 04 MAC: c84c.7596.e7c1
88E6095 rev 2 Ethernet @ index 03 MAC: c84c.7596.e7c0
88E6095 rev 2 Ethernet @ index 02 MAC: c84c.7596.e7bf
88E6095 rev 2 Ethernet @ index 01 MAC: c84c.7596.e7be
y88acs06 rev16 Gigabit Ethernet @ index 00 MAC: c84c.7596.e7c6
Verify the activation-key, it might take a while...
Running Permanent Activation Key: 0x3021cd54 0x20efac90 0xc852410c 0xb95cd094 0xc108009a
Licensed features for this platform:
Maximum Physical Interfaces : 8 perpetual
VLANs : 3 DMZ Restricted
Dual ISPs : Disabled perpetual
VLAN Trunk Ports : 0 perpetual
Inside Hosts : 10 perpetual
Failover : Disabled perpetual
Encryption-DES : Enabled perpetual
Encryption-3DES-AES : Enabled perpetual
AnyConnect Premium Peers : 2 perpetual
AnyConnect Essentials : Disabled perpetual
Other VPN Peers : 10 perpetual
Total VPN Peers : 12 perpetual
Shared License : Disabled perpetual
AnyConnect for Mobile : Disabled perpetual
AnyConnect for Cisco VPN Phone : Disabled perpetual
Advanced Endpoint Assessment : Disabled perpetual
UC Phone Proxy Sessions : 2 perpetual
Total UC Proxy Sessions : 2 perpetual
Botnet Traffic Filter : Disabled perpetual
Intercompany Media Engine : Disabled perpetual
Cluster : Disabled perpetual
This platform has a Base license.
Encryption hardware device : Cisco ASA-5505 on-board accelerator (revision 0x0)
Boot microcode : CN1000-MC-BOOT-2.00
SSL/IKE microcode : CNLite-MC-SSLm-PLUS-2.03
IPSec microcode : CNlite-MC-IPSECm-MAIN-2.08
Cisco Adaptive Security Appliance Software Version 9.0(1)
****************************** Warning *******************************
This product contains cryptographic features and is
subject to United States and local country laws
governing, import, export, transfer, and use.
Delivery of Cisco cryptographic products does not
imply third-party authority to import, export,
distribute, or use encryption. Importers, exporters,
distributors and users are responsible for compliance
with U.S. and local country laws. By using this
product you agree to comply with applicable laws and
regulations. If you are unable to comply with U.S.
and local laws, return the enclosed items immediately.
A summary of U.S. laws governing Cisco cryptographic
products may be found at:
http://www.cisco.com/wwl/export/crypto/tool/stqrg.html
If you require further assistance please contact us by
sending email to export@cisco.com.
******************************* Warning *******************************
This product includes software developed by the OpenSSL Project
for use in the OpenSSL Toolkit (http://www.openssl.org/)
Copyright (C) 1995-1998 Eric Young (eay@cryptsoft.com)
All rights reserved.
Copyright (c) 1998-2011 The OpenSSL Project.
All rights reserved.
This product includes software developed at the University of
California, Irvine for use in the DAV Explorer project
(http://www.ics.uci.edu/~webdav/)
Copyright (c) 1999-2005 Regents of the University of California.
All rights reserved.
Restricted Rights Legend
Use, duplication, or disclosure by the Government is
subject to restrictions as set forth in subparagraph
(c) of the Commercial Computer Software - Restricted
Rights clause at FAR sec. 52.227-19 and subparagraph
(c) (1) (ii) of the Rights in Technical DataSoftware clause at DFARS sec. 252.227-7013.
Cisco Systems, Inc.
170 West Tasman Drive
San Jose, California 95134-1706
Reading from flash...
!.
Cryptochecksum (unchanged): 2013e7a5 6a354989 98725b71 858eed96
Type help or '?' for a list of available commands.
ciscoasa>
For this scenario, we'll be doing the latter and here are the steps for booting an ASA image file when in ROMMON mode:
Steps ROMMON Command
1. Interrupt the bootup sequence Press Esc or Break at the appropriate time
2. Identify an ASA interface where the rommon>interface <physical-name>
TFTP server is located.
3. Assign an IP address to the ASA interface. rommon>address <ip-address>
4. Assign a default gateway (optional) rommon>gateway <ip-address>
5. Identify the TFTP server address. rommon>server <ip-address>
6. Identify the image filename. rommon>file <filename>
7. Test connectivity to the TFTP server. rommon>ping <ip-address>
8. Issue the tftpdnld command rommon>tftpdnld
Evaluating BIOS Options ...
Launch BIOS Extension to setup ROMMON
Cisco Systems ROMMON Version (1.0(12)13) #0: Thu Aug 28 15:55:27 PDT 2008
Platform ASA5505
Use BREAK or ESC to interrupt boot.
Use SPACE to begin boot immediately.
Boot in 8 seconds // HIT ESC KEY
Boot interrupted.
Ethernet0/0 // CONNECTED TO FTP SERVER
MAC Address: c84c.7596.e7c6
Link is UP
Use ? for help.
rommon #0> ?
Variables: Use "sync" to store in NVRAM
ADDRESS= <addr> local IP address
CONFIG= <name> config file path/name
GATEWAY= <addr> gateway IP address
IMAGE= <name> image file path/name
LINKTIMEOUT= <num> Link UP timeout (seconds)
PKTTIMEOUT= <num> packet timeout (seconds)
PORT= <name> ethernet interface port
RETRY= <num> Packet Retry Count (Ping/TFTP)
SERVER= <addr> server IP address
VLAN= <num> enable/disable DOT1Q tagging on the selected port
Commands:
? valid command list
address <addr> local IP address
boot <args> boot an image, valid args are:
- "image file spec" and/or
- "cfg=<config file spec>"
clear clear interface statistics
confreg <value> set hex configuration register
dev display platform interface devices
erase <arg> erase storage media
file <name> application image file path/name
gateway <addr> gateway IP address
gdb <cmd> edit image gdb settings
help valid command list
history display command history
interface <name> ethernet interface port
no <feat> clear feature settings
ping <addr> send ICMP echo
reboot halt and reboot system
reload halt and reboot system
repeat <arg> repeat previous command, valid arguments:
- no arg: repeat last command
- number: index into command history table
- string: most recent 1st arg match in command history table
reset halt and reboot system
server <addr> server IP address
set display all variable settings
show <cmd> display cmd-specific information
sync save variable settings in NVRAM
tftpdnld TFTP download
timeout <num> packet timeout (seconds)
trace toggle packet tracing
unset <varname> unset a variable name
rommon #1> address 192.168.1.1
rommon #2> server 192.168.1.2
rommon #3> file asa901-k8.bin
rommon #4> ping 192.168.1.2
Sending 20, 100-byte ICMP Echoes to 192.168.1.2, timeout is 4 seconds:
?!!!!!!!!!!!!!!!!!!!
Success rate is 95 percent (19/20)
rommon #5> tftpdnld
ROMMON Variable Settings:
ADDRESS=192.168.1.1
SERVER=192.168.1.2
GATEWAY=0.0.0.0
PORT=Ethernet0/0
VLAN=untagged
IMAGE=asa901-k8.bin
CONFIG=
LINKTIMEOUT=20
PKTTIMEOUT=4
RETRY=20
tftp asa901-k8.bin@192.168.1.2
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
<output truncated>
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
Received 27260928 bytes
Launching TFTP Image...
Cisco Security Appliance admin loader (3.0) #0: Fri Oct 26 16:36:37 PDT 2012
Platform ASA5505
Loading...
IO memory blocks requested from bigphys 32bit: 9928
Àdosfsck 2.11, 12 Mar 2005, FAT32, LFN
Starting check/repair pass.
Starting verification pass.
/dev/hda1: 392 files, 26848/31033 clusters
dosfsck(/dev/hda1) returned 0
Processor memory 343932928, Reserved memory: 62914560
Total SSMs found: 0
Total NICs found: 10
88E6095 rev 2 Gigabit Ethernet @ index 09 MAC: 0000.0003.0002
88E6095 rev 2 Ethernet @ index 08 MAC: c84c.7596.e7c5
88E6095 rev 2 Ethernet @ index 07 MAC: c84c.7596.e7c4
88E6095 rev 2 Ethernet @ index 06 MAC: c84c.7596.e7c3
88E6095 rev 2 Ethernet @ index 05 MAC: c84c.7596.e7c2
88E6095 rev 2 Ethernet @ index 04 MAC: c84c.7596.e7c1
88E6095 rev 2 Ethernet @ index 03 MAC: c84c.7596.e7c0
88E6095 rev 2 Ethernet @ index 02 MAC: c84c.7596.e7bf
88E6095 rev 2 Ethernet @ index 01 MAC: c84c.7596.e7be
y88acs06 rev16 Gigabit Ethernet @ index 00 MAC: c84c.7596.e7c6
Verify the activation-key, it might take a while...
Running Permanent Activation Key: 0x3021cd54 0x20efac90 0xc852410c 0xb95cd094 0xc108009a
Licensed features for this platform:
Maximum Physical Interfaces : 8 perpetual
VLANs : 3 DMZ Restricted
Dual ISPs : Disabled perpetual
VLAN Trunk Ports : 0 perpetual
Inside Hosts : 10 perpetual
Failover : Disabled perpetual
Encryption-DES : Enabled perpetual
Encryption-3DES-AES : Enabled perpetual
AnyConnect Premium Peers : 2 perpetual
AnyConnect Essentials : Disabled perpetual
Other VPN Peers : 10 perpetual
Total VPN Peers : 12 perpetual
Shared License : Disabled perpetual
AnyConnect for Mobile : Disabled perpetual
AnyConnect for Cisco VPN Phone : Disabled perpetual
Advanced Endpoint Assessment : Disabled perpetual
UC Phone Proxy Sessions : 2 perpetual
Total UC Proxy Sessions : 2 perpetual
Botnet Traffic Filter : Disabled perpetual
Intercompany Media Engine : Disabled perpetual
Cluster : Disabled perpetual
This platform has a Base license.
Encryption hardware device : Cisco ASA-5505 on-board accelerator (revision 0x0)
Boot microcode : CN1000-MC-BOOT-2.00
SSL/IKE microcode : CNLite-MC-SSLm-PLUS-2.03
IPSec microcode : CNlite-MC-IPSECm-MAIN-2.08
Cisco Adaptive Security Appliance Software Version 9.0(1)
****************************** Warning *******************************
This product contains cryptographic features and is
subject to United States and local country laws
governing, import, export, transfer, and use.
Delivery of Cisco cryptographic products does not
imply third-party authority to import, export,
distribute, or use encryption. Importers, exporters,
distributors and users are responsible for compliance
with U.S. and local country laws. By using this
product you agree to comply with applicable laws and
regulations. If you are unable to comply with U.S.
and local laws, return the enclosed items immediately.
A summary of U.S. laws governing Cisco cryptographic
products may be found at:
http://www.cisco.com/wwl/export/crypto/tool/stqrg.html
If you require further assistance please contact us by
sending email to export@cisco.com.
******************************* Warning *******************************
This product includes software developed by the OpenSSL Project
for use in the OpenSSL Toolkit (http://www.openssl.org/)
Copyright (C) 1995-1998 Eric Young (eay@cryptsoft.com)
All rights reserved.
Copyright (c) 1998-2011 The OpenSSL Project.
All rights reserved.
This product includes software developed at the University of
California, Irvine for use in the DAV Explorer project
(http://www.ics.uci.edu/~webdav/)
Copyright (c) 1999-2005 Regents of the University of California.
All rights reserved.
Restricted Rights Legend
Use, duplication, or disclosure by the Government is
subject to restrictions as set forth in subparagraph
(c) of the Commercial Computer Software - Restricted
Rights clause at FAR sec. 52.227-19 and subparagraph
(c) (1) (ii) of the Rights in Technical DataSoftware clause at DFARS sec. 252.227-7013.
Cisco Systems, Inc.
170 West Tasman Drive
San Jose, California 95134-1706
Reading from flash...
!.
Cryptochecksum (unchanged): 2013e7a5 6a354989 98725b71 858eed96
Type help or '?' for a list of available commands.
ciscoasa>
Subscribe to:
Posts (Atom)